Deploy Azure Application Gateway V2 with http to https redirect
Azure Application Gateway is an advance type of load-balancer. Where an Azure Load-balancer routes traffic on the transport layer (OSI Layer 4 | TCP + UDP) the Application Gateway is a way more advanced load-balancer. It can route based on URL as well on path’s. On top of that it can do much more, like SSL offloading, autoscaling, redirection, multiple site hosting and the most import of all, it can include a web application firewall (WAF). Today we will be deploying an Azure Application Gateway V2
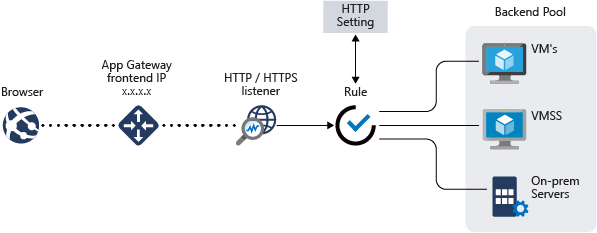
With all the features that the Azure application gateway provides, we should be able to setup multiple websites listening on different ports and url’s behind one Azure Application Gateway with just one external IP address.
With this guide you should be able to setup an application gateway with multiple site hostname match. For testing / demo purposes we will configure first http, then https and as a last step will setup the redirect.
So what are we going to setup:
- Deploy Azure application gateway
- Configure 1 external URL
- We will redirect port 80 to 443
For this guide the VNET, subnets and the virtual machine hosting the website have already been deployed. During this guide we will not deploy a Web Application Firewall.
Let’s get started with the deployment and configuration of the Azure Application Gateway.
Prerequisites:
– Dedicated subnet for the Azure Application Gateway
– Connectivity between the AGW and the virtual machines.
– SSL Certificate
– DNS Access
STEP 1: Create the application gateway
From the Azure Portal, use the top search bar for Application Gateway.
On the Load balancing | Application Gateway page click create

From the new page select the following options:
- Subscription
- Resource Group
- Application gateway name
- Region
- Tier (select Standard v2 or with Web Application Firewall V2)
- Enable Autoscaling (for this manual I selected no, but for production purposes always use Yes)
- Virtual Network and Subnet

Now select the desired Frontend IP address type, usually Public is used. Create a new public IP when there is none available.

From the new page we are going to add a Backend

Click on Add a routing rule

Give your new routing rule a name, since we are going to route http first, lets name it http. Give your rule a priority.
First we are going to create the listener. Give your listener a name, in this case the URL name with the listening port. Make sure to select Multi site for the listener type, and fill in the required hostname.

Now click on Backend targets, and select the just created backend pool. For the backend settings click on Add new
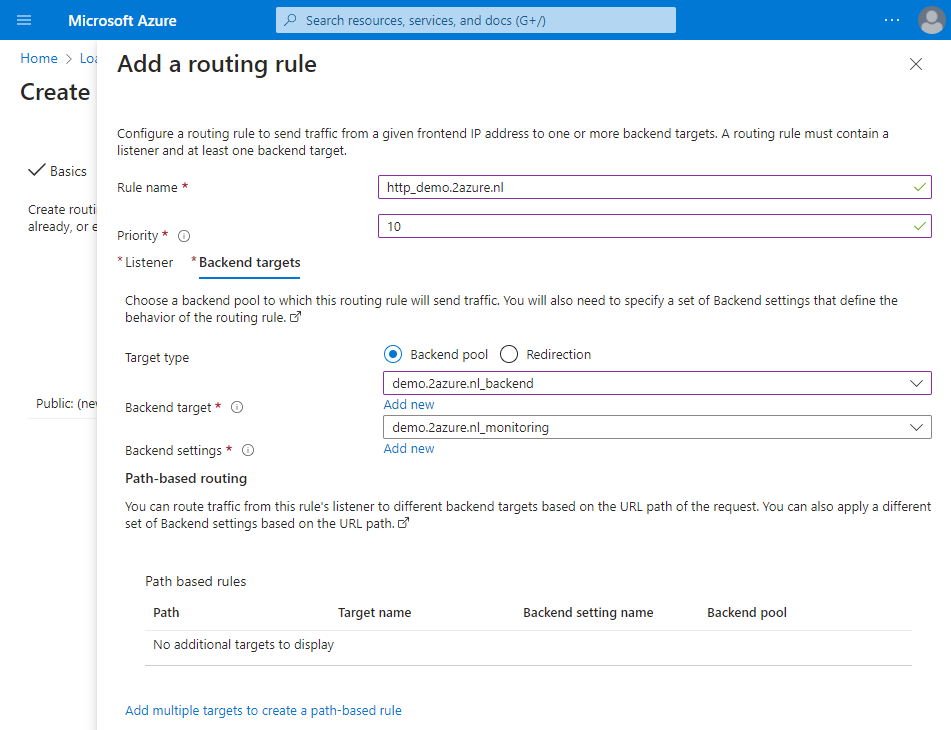
Now give your backend settings a name, and change the settings to your needs. Usually you can select the backend protocol, and leave the rest default. Click save to go back to the last page, and click save again.

The result should look like this. Click Review + Create.
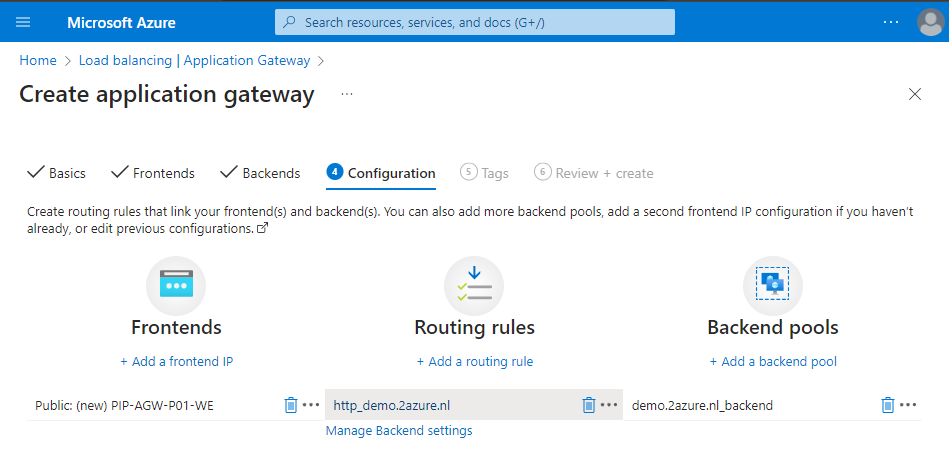
Now verify all settings and click Create when ready.
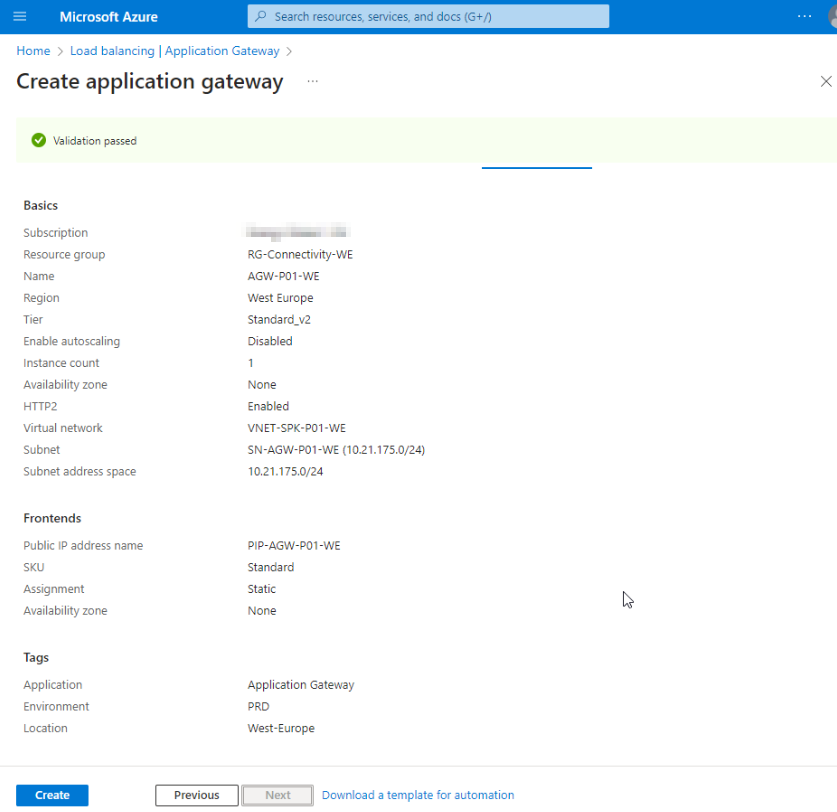
When the deployment is finished, we can lookup the public IP from the just create application gateway from the overview page and create a DNS entry for the selected domain.

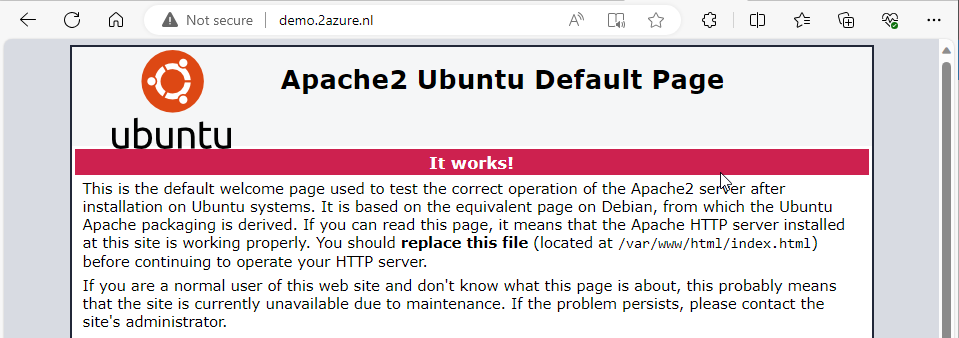
Now lets try to connect to the website, assuming you have something running already. In this case demo.2azure.nl.
STEP 2: Create HTTPS listener
Now go back to your resource. Go to Listeners, and click on Add listener. Keep the name the same as with the HTTP listener, except for the port, change it to 443. As you can see, you now get the option to add a Certificate. Upload a certificate in the PFX format. If you didn’t get an PFX, you can change the format of your SSL sertificate with OpenSSL for Windows of Linux. Make sure to change the Listener type to Multi site and fill in the host name. Click Add when ready.

Now go to Rules, and click on + Routing rule

Fill in the rule name matching the naming convention from the http rule, give it a different priority and select the just created listener.

Go to the Backend Targets tab, and select the same backend target and settings from the http rule. Save when ready.

Now go ahead and test the HTTPS listener.

STEP 3: Change HTTP listener to redirect
Now go to Rules again. Click on your http listener.

Go to Backend targets and change the Target type to Redirection.
Change the listener to redirect to your https listener.

This change might take a minute or 5, but after that, your http request will be redirected to https.
