Microsoft Entra (Azure AD) Domain Services an option or not?
Frequently I get the question, how are we going to manage our legacy Azure IaaS servers? Should we deploy domain controllers? or should we setup a VPN connection with our on-premise environment?
Before we can start answering these questions we will need to learn more about ME DS.
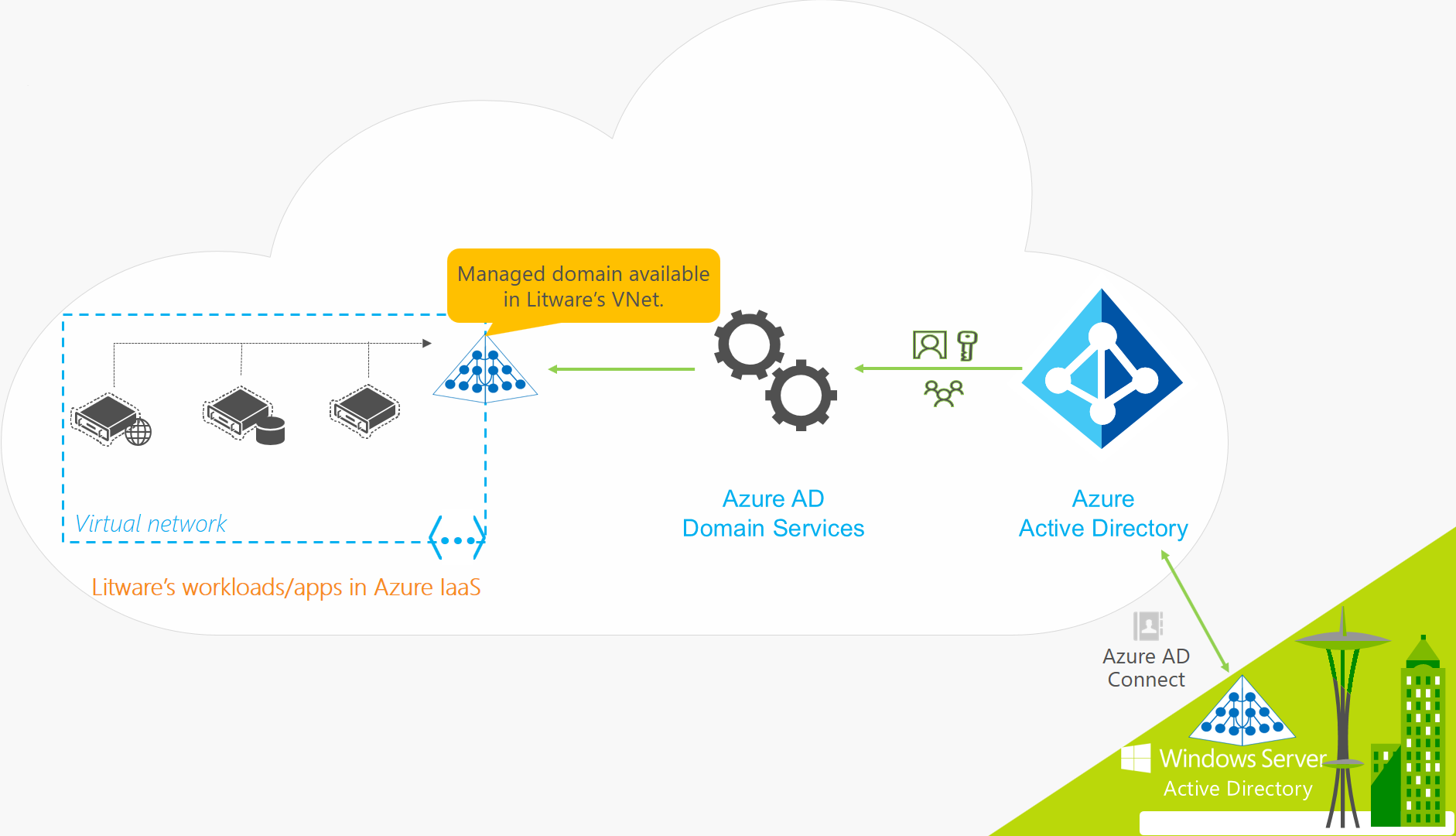
Microsoft Entra Domain Services provides managed domain services such as domain join, group policy, LDAP, Kerberos/NTLM authentication that are the same as traditional domain controllers. You can consume these domain services without the need for you to deploy, manage, and patch domain controllers in the cloud. Microsoft Entra Domain Services integrates with your existing Entra ID tenant, thus making it possible for users to log in using their corporate credentials. The ME DS is available in a VNet of your choice.

ME DS works with cloud-only or synced with on-premise AD. Important to know is that Password hash synchronization is mandatory for hybrid organizations to use Microsoft Entra domain services. This requirements is because users credentials are needed in the managed domain to authenticate using NTML or Kerberos.
- Contoso’s IT administrator does not need to manage, patch, or monitor this domain or any domain controllers for this managed domain.
- There is no need to manage AD replication for this domain. User accounts, group memberships, and credentials from Contoso’s Microsoft Entra tenant are automatically available within this managed domain.
- Since the domain is managed by Microsoft Entra Domain Services, Contoso’s IT administrator does not have Domain Administrator or Enterprise Administrator privileges on this domain.
| Azure Active Directory Domain Services advantages |
| No need to manage, patch or monitor this domain (controllers) |
| No AD replication required, user accounts, group memberships and credentials from the Azure AD tenant are automatically available within this domain. |
| Secure, since it is managed, your admin account does not have Domain Administrator or Enterprise Administrator privileges. |
| Redundant by default (High available) |
| No need for a VPN tunnel with on-premise |
| Traditional domain controllers advantages |
| Flexible, better administration possibilities using GPO, OU and schemas |
| Can be stretched over multiple Azure regions and on-premise |
| No need to synchronize passwords to Azure AD |
| Full Domain Administrator and Enterprise Administrator privileges available |
| Users and groups can be modified directly in AD |
If you’re moving to Azure and you need to lift and shift a few legacy application servers it might be mandatory to replace your domain controllers with Microsoft Entra DS. If you need to maintain a lot of servers, or you are going to work in a full hybrid configuration with a VPN it might be good to stick with traditional domain controllers.
Want to help improve this article? please let me know by replying on this article.